I’ve spent years studying how counterfeiters break security features that were supposed to be unbreakable.
You’re probably here because you want to know what actually makes a hologram secure. Not the marketing claims. The real technology.
Here’s the truth: standard holograms don’t cut it anymore. Counterfeiters have figured them out. The global economy loses billions every year because security features that looked impressive five years ago are now easy to fake.
GFX Robotection is changing that with technologies most people don’t even know exist yet.
I dug into the optical physics and material science behind next-generation holograms. The ones that actually stop counterfeiters cold.
This article breaks down the specific technologies that make modern holograms virtually impossible to replicate. I’m talking about nanostructures, digital integration, and manufacturing processes that go way beyond what you see on a credit card.
You’ll learn how to spot the difference between a hologram that just looks fancy and one that’s built with real security. No fluff about “advanced protection.” Just the actual science and tech that makes counterfeiting these things nearly impossible.
By the end, you’ll know exactly which features matter and why they work.
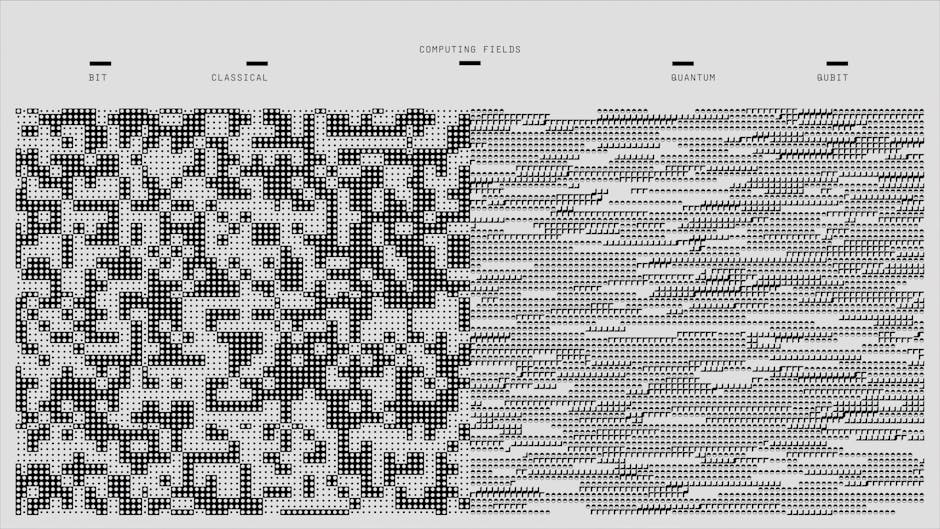
The Foundation: What Makes a Hologram ‘Secure’?
I remember the first time someone handed me what they thought was a secure hologram.
It was on a product label. Shiny. Reflective. Had that rainbow effect when you tilted it. The client was convinced they’d solved their counterfeiting problem.
I took one look and knew they were in trouble.
Here’s what most people don’t understand about security holograms. They’re not just pretty 3D images that look cool under light. A real security hologram is an optical device built at microscopic levels. We’re talking about structures so small you need specialized equipment just to see them properly.
The security doesn’t come from the hologram looking fancy. It comes from how impossibly difficult it is to copy the light-diffracting structure itself.
Think about it this way. When light hits a security hologram, it bounces off thousands of microscopic patterns etched into the material. Those patterns determine what you see. Change even one tiny element and the whole thing looks different.
Now here’s where it gets interesting.
Those older 2D and 3D holograms? The ones you still see on some products? They’re basically worthless now for anything valuable. Counterfeiters figured them out years ago. You can buy the equipment to copy them online for a few thousand dollars (sometimes less if you know where to look).
I’ve seen knockoffs that are so close to the original that even trained inspectors struggle to tell the difference.
So what changed?
Modern security moved beyond simple visual tricks. The holograms we use at gfxrobotection rely on optical structures that require equipment most counterfeiters will never access. We’re talking about machines that cost hundreds of thousands of dollars and need clean room environments to operate.
The barrier isn’t just money either. It’s expertise. Knowledge. Access to specific materials that aren’t sitting on Amazon waiting to be ordered.
That’s the principle behind real holographic security. Make the replication process so complex and expensive that it’s not worth attempting. Because which technology creates holograms Gfxrobotection matters less than understanding why certain methods work and others don’t.
Core Technology #1: Electron-Beam (E-Beam) Lithography
Let me show you how the most secure holograms get made.
E-Beam lithography uses a focused beam of electrons to etch patterns onto a master hologram plate. Think of it like drawing with a pencil that’s impossibly small.
How small?
We’re talking nanometers. That’s billionths of a meter.
This matters because these features are smaller than the wavelength of light itself. When you create structures that tiny, you get optical effects that simply can’t exist any other way. The revolutionary advancements in gaming technology, particularly with innovations like Gfxrobotection, are enabling developers to create intricate visual effects at scales smaller than the wavelength of light, unlocking a realm of optical possibilities that redefine our gaming experiences.
Here’s what that means for security.
You can’t copy these holograms with a camera. You can’t scan them with a laser. You can’t reproduce them with mechanical tools (no matter how precise those tools are).
The physics just doesn’t allow it.
When you look at which technology creates holograms gfxrobotection, E-Beam stands out because of what it lets you see:
- Ultra-high-resolution images that stay sharp even under magnification
- Hidden nano-text that’s only readable with a microscope
- Complex kinetic effects that shift and move as you tilt the hologram
That last one is where counterfeiters give up.
The movement patterns you see in an E-Beam hologram come from the precise arrangement of billions of nano-structures. Getting even one layer wrong breaks the entire effect.
I’ve watched people try to fake these. They get close on static images sometimes. But the moment you add motion? It falls apart.
That’s the point.
Core Technology #2: Dot-Matrix Origination

Here’s where things get interesting.
Most people think holograms are just fancy stickers. Something you slap on a product and call it secure.
They’re wrong.
Dot-Matrix origination works differently. We’re talking about computer-controlled lasers that engrave hundreds of thousands of individual dots onto a surface. Each dot sits at a specific angle. Each one creates what’s called a diffraction grating.
Think of it this way. A basic hologram might use a simple pattern you could theoretically copy. Dot-Matrix? It’s built on math so complex that replication becomes nearly impossible.
The security doesn’t come from what you see. It comes from what you can’t replicate.
A counterfeiter can scan the final image all day long. They’ll get a picture. But they won’t get the underlying mathematical model that determines where each of those dots goes and at what angle. That requires proprietary software and serious computational power (the kind most counterfeiters don’t have access to).
Now compare this to traditional printing methods. Standard printing lays ink on a surface. You scan it, you copy it. Done. I cover this topic extensively in Gfxrobotection Ai Graphics Software From Gfxmaker.
Dot-Matrix versus traditional security printing? It’s not even close.
Here’s what Dot-Matrix creates:
- Animated movements that shift as you tilt the hologram
- Brilliant color transitions that change with viewing angle
- Guilloché patterns with intricate geometric designs
These effects tell you immediately which technology creates holograms gfxrobotection uses for authentication. You can see the difference with your own eyes.
The gfxrobotection ai software by gfxmaker calculates every single dot placement. That’s not something you reverse engineer in a garage.
That’s the barrier counterfeiters can’t cross.
The Multi-Layered Defense: Combining Physical and Digital Security
You can see a hologram on a product. That’s the obvious part.
What you can’t see is where the real protection lives.
I’m talking about the hidden layers that counterfeiters can’t replicate. The stuff that sits beneath the surface, waiting to catch someone who thinks they’re clever enough to fake it. In a world where counterfeiters constantly evolve, the implementation of advanced measures like Robotic Software Gfxrobotection reveals the hidden layers of authenticity that remain impervious to imitation, ensuring that what lies beneath the surface is truly safeguarded from those who underestimate its complexity.
Let me walk you through what actually works.
Covert Features That Matter
Micro-text is your first line of hidden defense. It looks like a solid line until you put it under magnification. Then you see text so small that standard printing can’t reproduce it.
UV-fluorescent inks take it further. They’re invisible under normal light but glow under specific wavelengths. You need the right equipment to even know they’re there.
Then there’s laser-viewable images. These only appear when you hit them with a laser at the correct angle. Good luck faking that in your basement.
Tamper-Evident Design
Here’s what I recommend for high-value items. Use holograms bonded to substrates that self-destruct on removal.
Try to peel one off and you’ll get a VOID pattern. Or the hologram fragments into pieces. Either way, you can’t reuse it on a counterfeit product.
This matters more than people think. A hologram that can be transferred is basically worthless (it’s just expensive decoration at that point).
The Smart Hologram Approach
This is where robotic software gfxrobotection comes into play. I go into much more detail on this in Which Ipad Should I Buy for Digital Art Gfxrobotection.
You embed serialized QR codes or NFC chips directly into the hologram structure. Each one links to a secure database. Anyone with a smartphone can verify authenticity in seconds.
Which technology creates holograms gfxrobotection uses depends on your security needs. But combining physical and digital verification gives you something counterfeiters can’t easily beat.
Scan the code. Check the database. Confirm the product is real.
That’s the kind of protection that actually stops fraud.
Practical Application: How to Spot a High-Security Hologram
You don’t need to be a forensics expert to tell if a hologram is legit.
I’m going to show you exactly what to look for.
Start with the basics. Tilt the item under light. A real high-security hologram shifts colors smoothly. You’ll see depth and movement (not just a flat, dull sticker that barely reflects).
Here’s what separates the real ones from the fakes.
Genuine holograms stack multiple features. You might see a 2D/3D effect combined with tiny moving dots. Look closer and you’ll spot micro-text that’s actually readable under magnification.
The payoff? You’ll catch counterfeits before they become your problem. Whether you’re verifying product authenticity or checking credentials, knowing which technology creates holograms gfxrobotection uses can save you from costly mistakes.
When you’re still not sure, go digital.
If there’s a QR code embedded in the hologram, scan it. This gives you instant verification against the manufacturer’s database. It’s the fastest way to confirm what you’re holding is real. To ensure the authenticity of your gaming gear, utilizing the Gfxrobotection Ai Software by Gfxmaker alongside the embedded QR code in the hologram provides a seamless verification process against the manufacturer’s database.
The bottom line is simple. Spend thirty seconds doing these checks and you’ll know what you’re dealing with.
The Future of Authentication is Layered and Complex
You now understand that real anti-counterfeit holograms aren’t built on one trick.
They rely on a suite of technologies working together. E-Beam lithography, Dot-Matrix, and digital integration create layers that counterfeiters can’t easily crack.
The problem keeps evolving. As counterfeiters get smarter, security has to stay ahead.
The answer is multi-layered complexity. When you combine nano-scale physical features with digital verification, you make replication economically unfeasible. Most counterfeiters won’t even try because the cost and technical barriers are too high.
True protection doesn’t come from a single feature.
It comes from a complete security strategy where the hologram acts as a visible and verifiable seal of authenticity. Each layer adds another obstacle that makes fraud harder to pull off.
Here’s what matters: The technologies exist to protect your products right now. The question is whether you’re using them before someone copies what you’ve built.
Start by evaluating your current authentication methods. Look for gaps where counterfeiters could slip through. Then build a layered approach that combines physical and digital verification.
The brands that survive are the ones that make counterfeiting too expensive and too difficult to bother with.

 Lorissa Ollvain writes the kind of practical tech applications content that people actually send to each other. Not because it's flashy or controversial, but because it's the sort of thing where you read it and immediately think of three people who need to see it. Lorissa has a talent for identifying the questions that a lot of people have but haven't quite figured out how to articulate yet — and then answering them properly.
They covers a lot of ground: Practical Tech Applications, Software Development Trends, Robotics and Automation Insights, and plenty of adjacent territory that doesn't always get treated with the same seriousness. The consistency across all of it is a certain kind of respect for the reader. Lorissa doesn't assume people are stupid, and they doesn't assume they know everything either. They writes for someone who is genuinely trying to figure something out — because that's usually who's actually reading. That assumption shapes everything from how they structures an explanation to how much background they includes before getting to the point.
Beyond the practical stuff, there's something in Lorissa's writing that reflects a real investment in the subject — not performed enthusiasm, but the kind of sustained interest that produces insight over time. They has been paying attention to practical tech applications long enough that they notices things a more casual observer would miss. That depth shows up in the work in ways that are hard to fake.
Lorissa Ollvain writes the kind of practical tech applications content that people actually send to each other. Not because it's flashy or controversial, but because it's the sort of thing where you read it and immediately think of three people who need to see it. Lorissa has a talent for identifying the questions that a lot of people have but haven't quite figured out how to articulate yet — and then answering them properly.
They covers a lot of ground: Practical Tech Applications, Software Development Trends, Robotics and Automation Insights, and plenty of adjacent territory that doesn't always get treated with the same seriousness. The consistency across all of it is a certain kind of respect for the reader. Lorissa doesn't assume people are stupid, and they doesn't assume they know everything either. They writes for someone who is genuinely trying to figure something out — because that's usually who's actually reading. That assumption shapes everything from how they structures an explanation to how much background they includes before getting to the point.
Beyond the practical stuff, there's something in Lorissa's writing that reflects a real investment in the subject — not performed enthusiasm, but the kind of sustained interest that produces insight over time. They has been paying attention to practical tech applications long enough that they notices things a more casual observer would miss. That depth shows up in the work in ways that are hard to fake.